Authorise your SOC to save your business: used countermeasures!
Every minute counts when a cyberattack hits.
Before an incident becomes a breach, before a suspicious signal becomes a crisis, one question matters: has your Security Operations Centre (SOC) been authorised to act?
Because even the best monitoring is powerless without one critical ingredient: the ability to trigger countermeasures instantly!
In today's threat landscape, attackers don't wait. Your SOC shouldn't either.
What is a countermeasure?
In the cybersecurity context, a countermeasure is any action take to counter a potential or confirmed threat that could negatively impact a business.
Such impacts may include financial losses, reputational damage, or operational disruptions.
Why are countermeasures essential in threat mitigation?
Countermeasures play a critical role in the mitigation because they are the actions or strategies used to reduce or eliminate the impact of identified threats and vulnerabilities.
They help prevent or minimise damage, ensure business continuity and protect against financial, operational, and reputational risks.
By implementing countermeasures, organisations proactively manage risks and maintain a secure environment.
Which countermeasures can the Thales SOC apply?
At Thales, our SOC teams have the ability to perform several first-line countermeasures to support our customers with immediate mitigation. These actions help reduce risk instantly and block attackers as soon as a threat is detected.
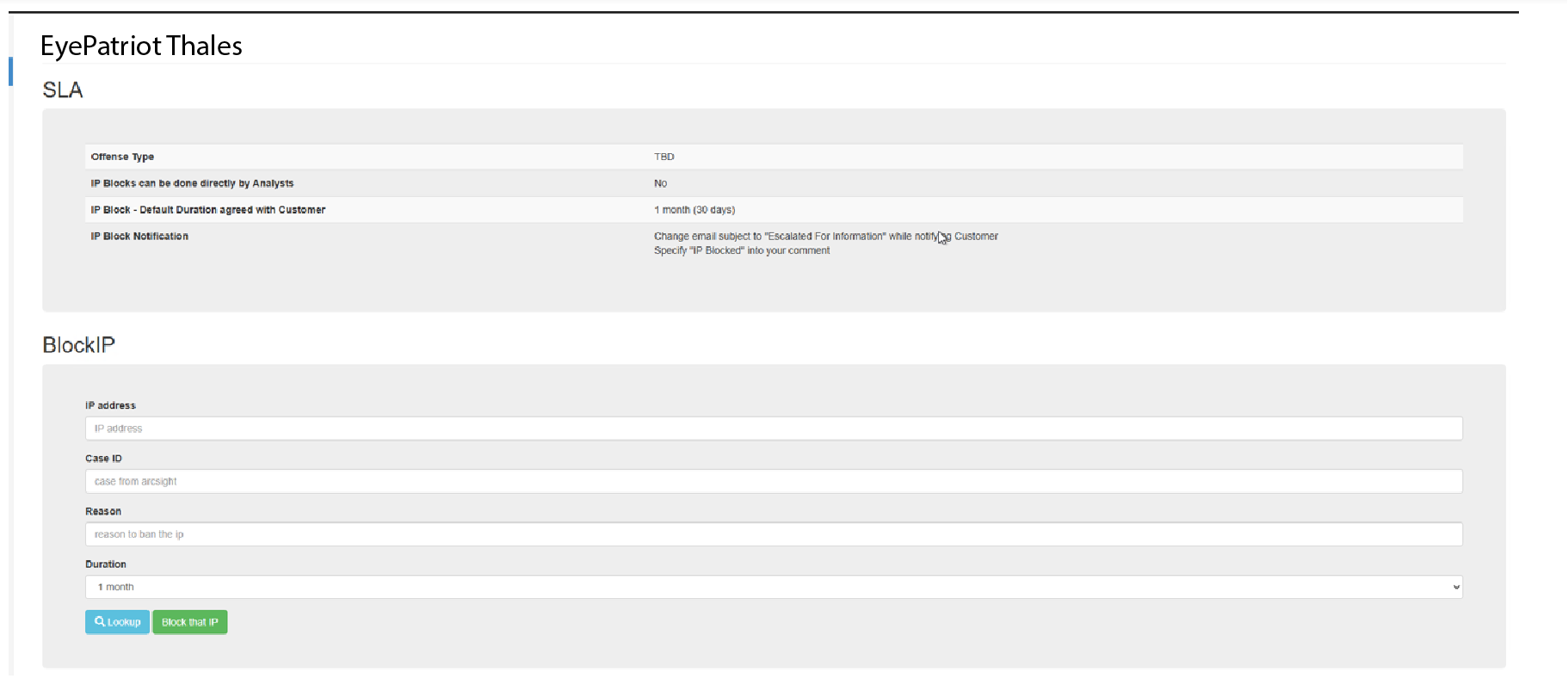
📌 Eyepatriot - Automated IP Blocking
As explained by Tanguy Pegeot, CSOC Analyst L2 at Thales in Luxembourg, the first coutermeasure is the ability to block IP addresses using our internally developed Eyepatriot. This tool generates a text file countaining all suspicious or malicious IPs detected on the customer's infrastructure. The customer's firewall then reads this file and updates its blacklist table to block all traffic from these IPs.
Below is an example of the form used to perform IP Blocking:
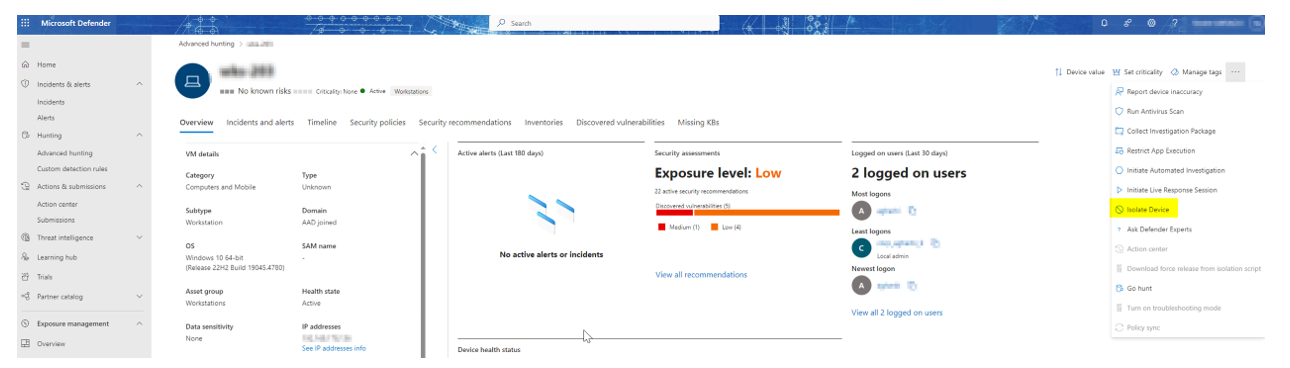
📌 Host isolation via EDR/XDR
If suspicious behaviour is detected on a host, isolating it via EDR/XDR capabilities can prevent threats from spreading across the network.
To enable this action, customers simply define the scope where isolation is allowed and grant the SOC permission to perform it.
Here is an example of how to isolate a devic eusing Defender XDR:
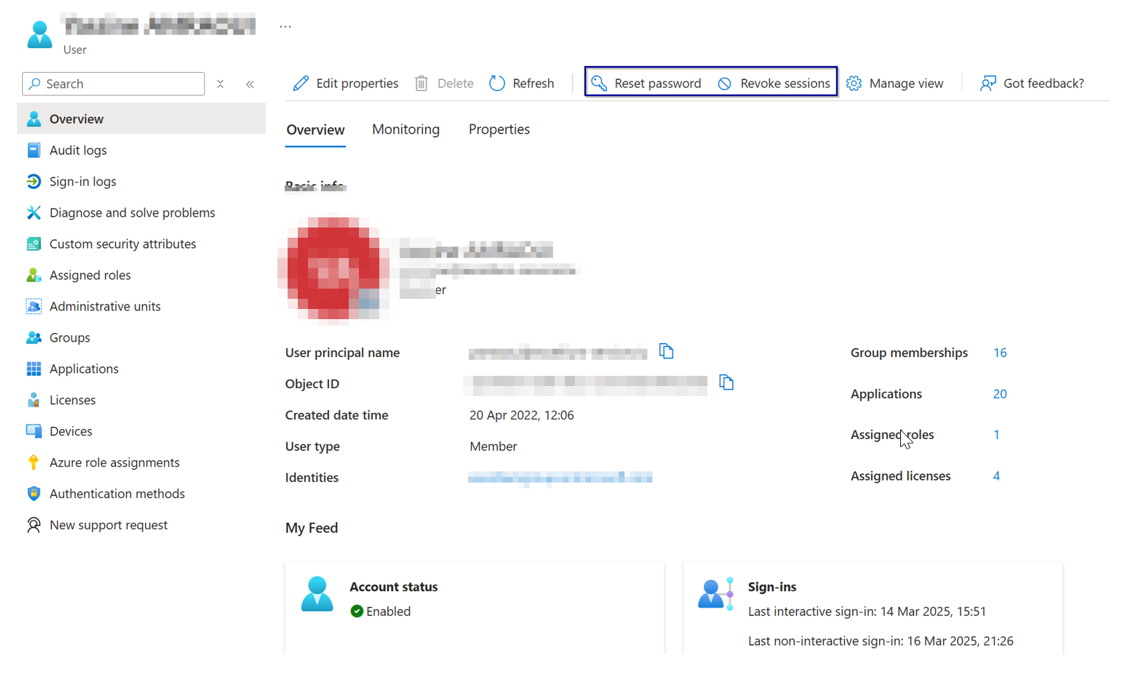
📌 User account revocation
If a user's account shows suspicious behaviour, the SOC may, when authorised, reset the user's password and revoke all active sessions until the situation is clarified. This prevents further malicious activity while the customer investigates.
Here is an example of how to revoke a user session from Azure AD:
Countermeasure example: a suspicious login pattern
Let's illustrate with a (fictional) case:
A suspicious geo-hopping pattern is detected for a user named "Bilbo". He usually connects from Belgium, yet within minutes, a login appears from Indonesia. This is either physically impossible or highly suspicious.
Further investigation reveals that the Indonesian IP is not part of a public VPN. We also spot numerous global login attempts targetting Bilbo's account.
This is a strong indicator of account compromise (botnet brute force attack).
Immediate actions taken:
▪️ All active user sessions are terminated.
▪️ Thes user's password is reset to a strong, random one.
The customer is advised to implement MFA (Multi Factor Authentication) implementationand take further security measures. At the same time, we detect the installation of one_ring.exe, known to be used by the malicious group "Sauron" for data exfiltration.Network traffic confirms communication with a command-and-control server.
Additional countermeasures applied:
▪️ The compromised device is isolated.
▪️ The malicious external IP is added to Eyepatriot for blocking.
▪️ The customer is instructed to clean the infected device.
These countermeasures prevented a data breach and the reputational damage that would have resulted from leaked data.
Why customers should enable SOC countermeasures?
Enabling countermeasures is not a technical detail, it is a business safeguard:
📌 Faster mitigation: Threats are contained instantly, preventing lateral movement and data loss
📌 Reduced business impact: Less downtime, fewer operational disruptions, and controlled financial risk.
📌 Time gained for DFIR: By freezing the attacker's actions, the SOC buys precious time for the Digital Forensics & Incident Response teams to investigate without pressure.
📌 Compliance & regulatory benefits: Fast response and documented actions support compliance with standards like ISO27001, NIS2, DORA, GDPR incident handling requirements.
📌 Stronger cyber resilience: Your organisation becomes harder to compromise and quicker to recover.
Authorising countermeasures = enabling your SOC to protect you when it matters most.
Conclusion
As shown, countermeasures are essential to protect infrastructure efficiently and quickly. It is vital that companies allow their 24/7 monitoring team (SOC or IT security) to perform these actions at any time.
This accelerates attack mitigation, buys time to investigate deeper threats, and strengthens overall protection.
Moreover, customers increasingly expert a proactive monitoring approach, and countermeasures are one of the best ways to deliver this level of protection.



