Bringing cybersecurity globally to critical and complex key activities
Europe News

BlackBasta Ransomware added Metro company to their victim list
On 8 November 2022, the cybercriminal group BlackBasta, which specialises in ransomware, claimed responsibility for an attack on the wholesale company Metro. The data they claimed to have stolen contained ID cards, agreements and passports. Metro's IT infrastructure was effectively blocked by the attack and the company was experiencing problems with in-store payments and delivery of online orders. Read more about it : here

KillNet want to conduct a DDoS campaign against any targets in Poland
On 15 November 2022, the pro-Russian hacktivist group KIlNet called on its affiliates to carry out a DDoS attack campaign on all possible organisations and entities in Poland and keep them inaccessible until 20 November 2022. In order to select targets, Killnet advises to perform a google search including "Online Poland, Login Poland, Poland commerce Online, Poland Health, Poland gov". Read more about it : here
BlackByte ransomware group added Peterson & Hansson Byggnads to their victims list
On November 5, 2022, the cybercriminal group BlackByte ransomware added the Swedish company Peterson & Hansson Byggnads to the list of its victims on its website. This construction company is based in Falkenberg and the data allegedly stolen from it includes invoices, employment contracts, and other administrative documents. No details on the damage caused by the ransomware have yet been communicated, and the company's site is still accessible. However, it is possible that some systems for making appointments, orders or even the means of communication have been affected. The impact would then be significant for the image of the company. Read more about it : here

DDoS attack on the websites of the Institute of National Remembrance
On 9 November 2022, starting at 11pm, a large-scale DDoS attack targeted the Polish website of the Institute of National Remembrance for several hours. On 10 November it was accessible again. The attack is believed to have taken down the websites linked to the Institute's homepage but spared the acrhives website. After investigation, it seems that the first attempts to attack the site failed on the morning of the 9th before resuming in the evening. Read more about it : here

Noname05716 targeting Polish science academy
On 8 November 2022, the pro-Russian hacktivist group Noname05716 claimed responsibility for a DDoS attack on the login page of the Nenetsky Institute of Experimental Biology website of the Polish Academy of Science. It is likely that this attack prevented people working at the institute from logging in for some time. This attack is part of a campaign of attacks by pro-Russian groups on Eastern European countries because of their commitment to the war in Ukraine against Russia. Read more about it : here

Spanish Ministry of Economy under cyber attack
On 21 November 2022, the Spanish Ministry of Economy and Digital Transformation has suffered a cyber attack. Indeed, employees reportedly found that their computer equipment was acting independently of their will. This suggests that attackers were able to carry out an intrusion attack, possibly using phishing as the initial entry point, and then drop a malicious payload allowing them to control the compromised computer remotely via the SARA network. The SARA network is the internal network of public institutions that allows for the rapid exchange of data between different departments. This type of network is often easy to use and considered by employees as a safe tool that they do not need to be wary of. Therefore, it is the perfect interface for an attacker to spread a malicious payload: fast, discreet and affecting all branches of public organisations. This attack was possibly aimed at espionage or data theft, as according to the media investigating the attack, the targeted sector was the analysis department, where all economic forecasts are produced and distributed. For the moment it is not yet possible to know whether data was stolen, or who was behind the attack. Nevertheless, it is likely that the attackers were not careful in their operation, as being detected by using live interfaces of a computer in use by employees crystallises a lack of professionalism. In parallel, it is noted that during October 2022, the General Council of the Judiciary detected a cyber attack that affected the Judicial Neutral Point (JNP), the telecommunications network that connects the judicial bodies to other state institutions. Read more about it : here

LockBit 3.0 european attacks second wave of claim
On 4 November 2022, the cybercriminal group LockBit 3.0 ransomware revealed a second wave of attack claims targeting three European companies and organisations, among others. This second wave of claims follows the first one on 29 October. The companies affected are as follows: Hettich, a manufacturing company from Netherland Continental, an IT provider company from Germany Tekniplex, an industrial of advanced plastic & rubber polymer technology company, from Belgium. These four companies were added to the victims at the same time, and each has between 1 and 9 days to meet LockBit's requirements. The impact of this attack could be significant for businesses and have a high financial cost if they agree to pay the ransom. The data stolen or the status of the companies' platforms has not been disclosed, but it is assumed that some of the victims' connected work features will be unusable. Read more about it : here, here, here and here

ViceSociety ransomware group claims responsibility for the cyberattack against Rhein-Pfalz-Kreis
On November 11, 2022, the cyber criminal group ViceSociety claimed responsibility for a ransomware attack against Rhein-Pfalz-Kreis, a German district in Rhineland-Palatinate. According to an official statement from the district, the attack took place on October 24, 2022. The district's website "https://www.rhein-pfalz-kreis.de/" is currently still inaccessible and indicates that it is unreachable following a cyber attack. Read more about it : here
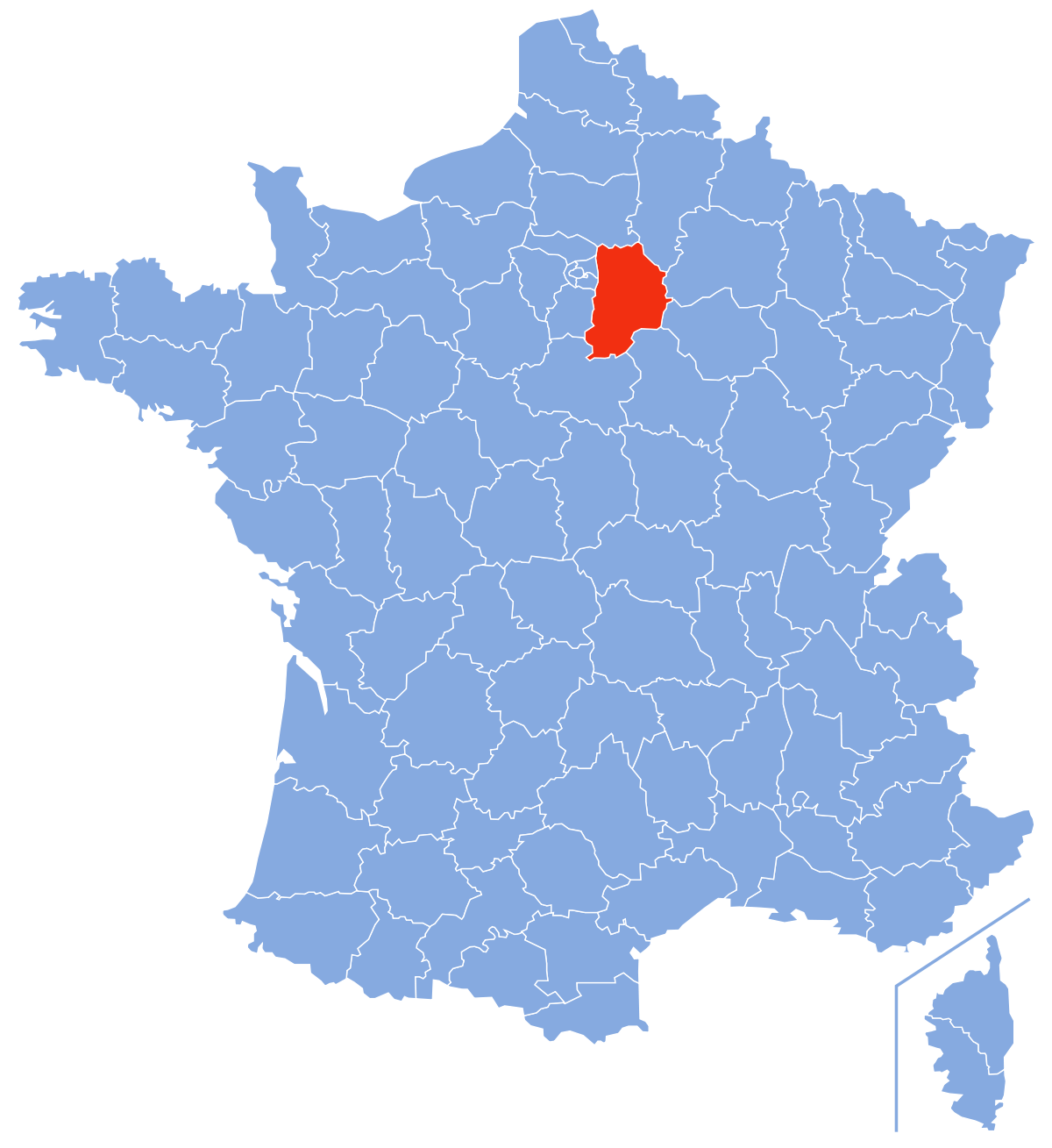
French Seine et Marne departement council victim of a cyber attack
On 8 November 2022, the departmental council of Seine et Marne in France announced that its IT infrastructure was unusable and blocked. Despite the intervention of a crisis unit, the department announced that it would not be able to resume normal activity for at least 6 weeks. IT staff were forced to shut down the servers that were attacked to prevent further damage. Departmental staff are unable to receive or send emails or access their internal files, which puts the administration in difficulty in providing social services to citizens. Read more about it : here

Schutznetze24 database on sell
On 22 November 2022, a cybercriminal identified as "Diana" posted the database of the German company schutznetze24 on a leaky forum. The company is a manufacturer of wire mesh for a variety of uses, from hanging livestock feed to securing construction sites. It claims to have 266,000 user records, including user ID, name, email address, password, etc. Read more about it : here