Thales Cyber Threat Intelligence services
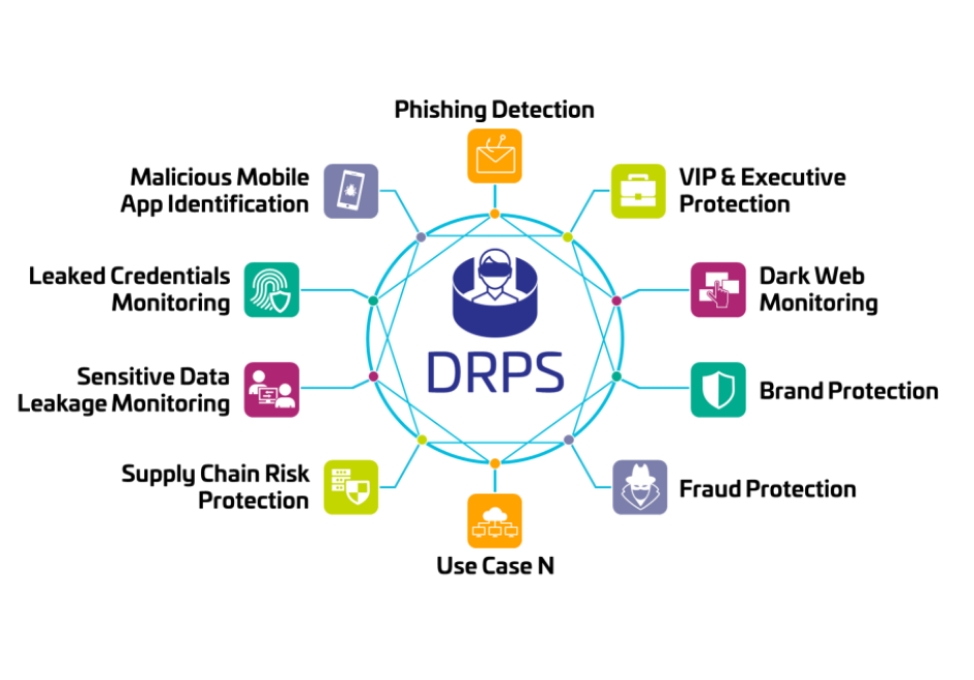
Capitalising on customized and specifically developped Thales feeds, as well as third party feeds as Mandiant, OSINT, CERT-IST, CERT-XLM, ESET, Filigran, ThreatQuotient, our CTI expert team worldwide is able to provide inputs, feeds and reports on the most valuable intelligence. Covering the wide range of cyber insights from Dark Web, Deep Web, blogs, social networks, Telegram, vulnerability feeds, SOCs, public sandbox, botnet, Customers, sensors, we can help you enhance your cyber strategy.
Our approach emphasizes cross-team collaboration, fostering the sharing of expertise among specialists.